𝙽𝙴𝚃𝚁𝙴𝚂𝙴𝙲 on Twitter: "The payload in “Exploit.class” spawns a shell and connects the input and output of the shell to a network socket, which gets connected back to the attacker's PC on
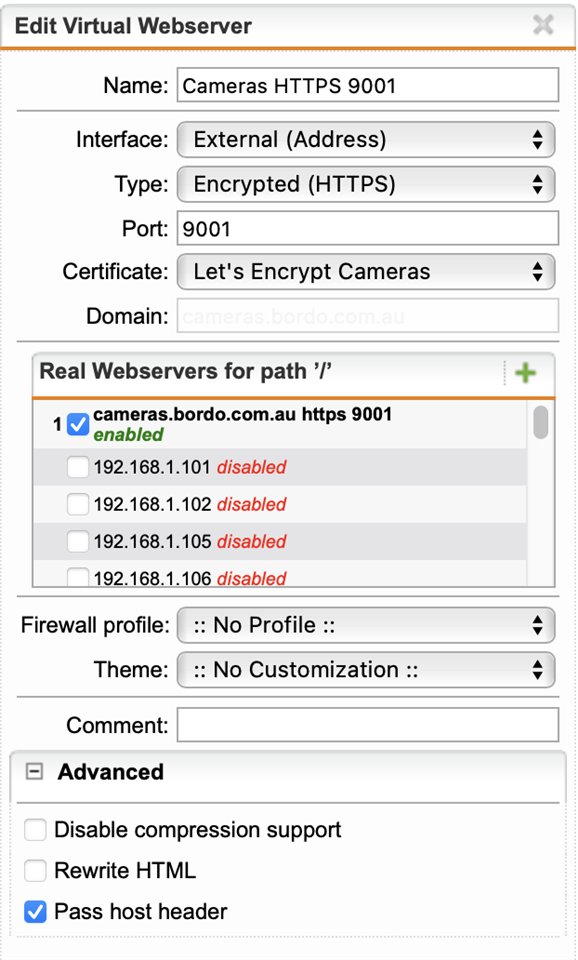
How to Pass all HTTP Headers (SecuritySpy iOS app) - Web Server Security - UTM Firewall - Sophos Community


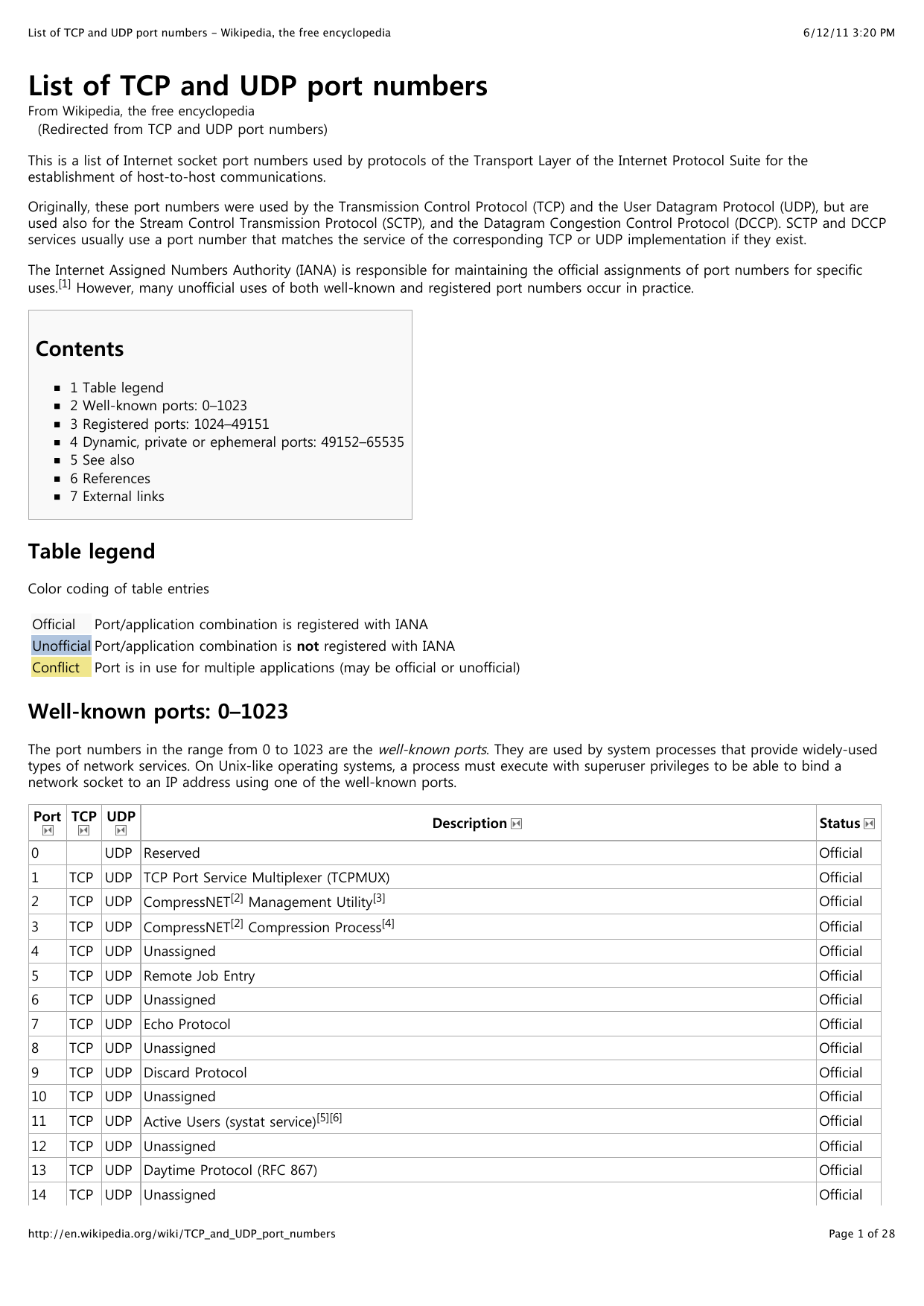
![ExpDev] Reverse TCP Shell. What is a Reverse Shell? | by bigb0ss | InfoSec Write-ups ExpDev] Reverse TCP Shell. What is a Reverse Shell? | by bigb0ss | InfoSec Write-ups](https://miro.medium.com/max/880/1*k9pux17STGOKcmp3DguMbw.png)